Cyberattacks, data breach, privacy of customers, citizens and employees’ personal information, together with the opportunities to create value from data and information held by organisations – are major drivers for organisations to implement a strategic approach to the governance of data and information as part of good corporate governance. Information Governance provides an overarching strategic framework for organisations seeking to control and secure information throughout their organisation, which both maximises the value of information and minimises the costs and risks of holding it.
Cyberattacks, data breach, privacy of customers, citizens and employees’ personal information, together with the opportunities to create value from data and information held by organisations – are major drivers for organisations to implement a strategic approach to the governance of data and information as part of good corporate governance. Information Governance provides an overarching strategic framework for organisations seeking to control and secure information throughout their organisation, which both maximises the value of information and minimises the costs and risks of holding it.
Twelve months ago, the Director-General of the Australian National Archives called for Chief Information Governance Officer positions to be created to lead the digital transformation in Federal government agencies. This article looks at different Information Governance leadership models being used in corporate and government organisations together with the views of Information Governance leaders in those organisations.
Who is responsible for data and information?
Typically, an organisation’s data and information is managed by various ‘owners’ and will vary according to the industry and organisational structure. In general, responsibility for data and information includes:
- Data – Chief Data Officer
- Data Analytics – Chief Data Scientist
- Customer data – Chief Digital Officer or Chief Marketing Officer
- eDiscovery – eDiscovery Counsel or General Counsel
- Privacy – Chief Privacy Officer
- Information Security – Chief Information Security Officer or Chief Information Officer
- Records & Information Management – Records and Information Manager
As the above lists highlights, the digital transformation over the past decade has created new roles and titles responding to the exponential growth of data to manage the risks and opportunities arising from data and information held by organisations. A key challenge for the continuing digital transformation and growth in data is for organisations to have internal organisational structures that align with organisational goals and objectives. In the context of responsibility for data and information, organisations require a cohesive governance structure to ensure data and information are effectively controlled and optimised to enable organisational objectives to be met. This is achieved through a formal Information Governance framework and effective Information Governance leadership.
The benefits of an Information Governance framework
A sound Information Governance framework is the critical foundation that enables organisations to govern and properly manage the information they hold. The benefits of a holistic approach include:
- senior-executive-level engagement and decision making on important strategic opportunities and risk mitigation issues concerning organisational information;
- increasing revenue and profits through the use of data analytics to develop or improve products or services, and/or through developing strategies to improve efficiencies and reduce costs;
- improved management of data, with more efficient retrieval of retained data;
- defensible destruction of redundant, outdated and trivial data/information (ROT), with an audit trail that can be relied upon in litigation or regulatory investigation;
- improved selection and return on investment (ROI) on new technology, appropriate to the organisation’s legal, compliance and business needs;
- comprehensive and aligned policies, processes and response plans – including comprehensive ICT security and privacy frameworks and breach response plans; and
- reduced costs and increased efficiencies arising from the implementation of an aligned strategy and policies, in contrast to the inefficiencies of the traditional fragmented siloed approach.
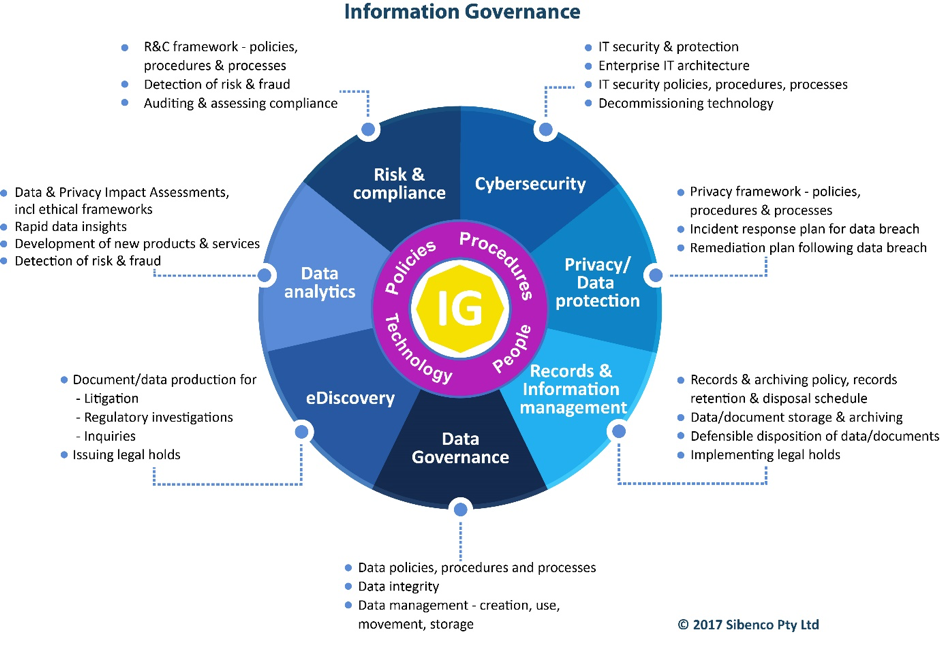
Information Governance leadership
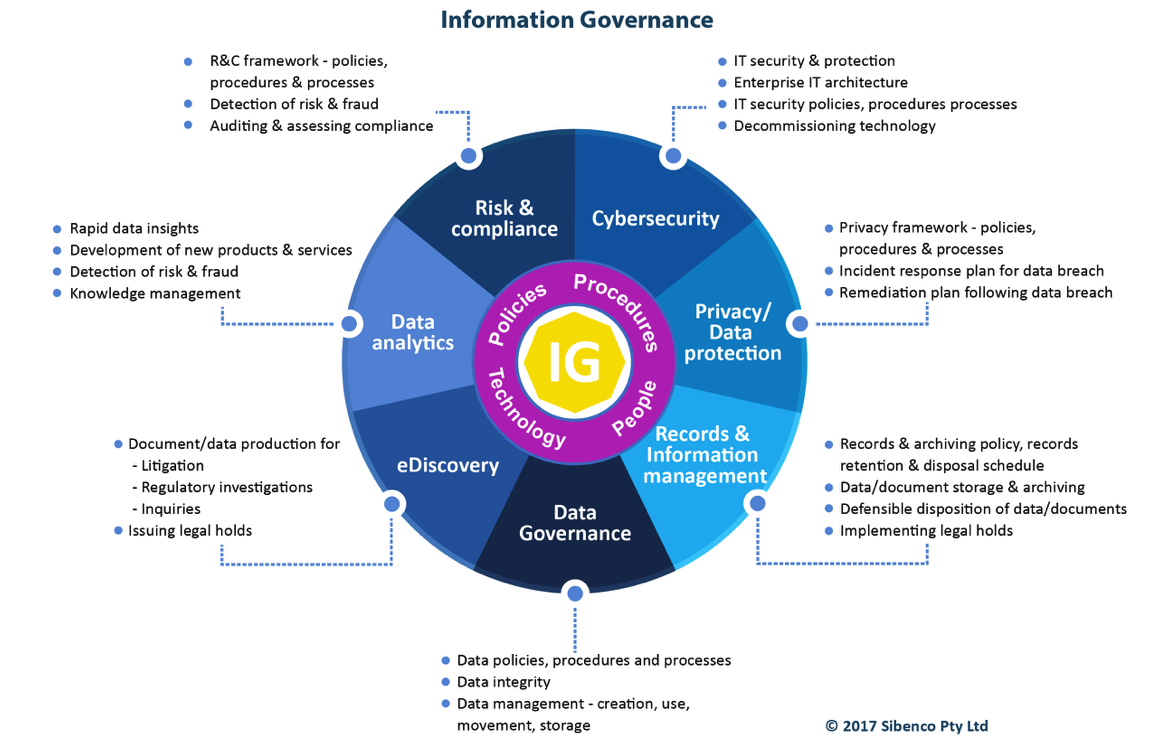
Information Governance leadership is about leading and collaborating with professionals from different disciplines across the ‘information silos’ to align activities and technologies to maximise the value of information while minimising the risks and costs of holding it. With the exponential growth in data and the risks and opportunities of data and information held within an organisation, effective Information Governance is a key factor in delivering strong Information Governance, which is part of good Corporate Governance. The diagram below illustrates the typical areas within an organisation where data and information are managed and governed by policies, procedures, technology and people.
Types of Information Governance leadership
The type of Information Governance leadership will vary between organisations, and are likely to depend on its strategic priorities, size, resources, and the current position of information management within it. Information Governance leadership types include: IG Steering Committee, C-level executive who also takes on responsibility of Information Governance in their portfolio of responsibilities; or a Chief Information Governance Officer
IG Steering committee
The IG Steering Committee is a committee made up of the relevant C-level and other executives and managers responsible for different areas of information and data management.
Ideally, the IG Steering Committee should be chaired by a C-level executive so that there is clear senior executive level support and direction. The direction and overarching strategy for Information Governance should be approved by the Board and CEO, who have ultimate responsibility for the governance of data and information. The Committee is responsible for setting priorities, such as deciding on pilot projects, carrying out reviews of implemented projects etc.
The position titles of the members of the Steering Committee may vary between organisations and will depend on factors such as the size and structure of the organisation and the stage of IG development within the organisation.
The composition of the IG Steering Committee may include the following – General Counsel (GC), Chief Information Security Officer (CISO), Chief Privacy Officer (CPO), Chief Data Officer (CDO), Chief Marketing Officer (CMO), Chief Data Scientist (CDS), Records & Information Manager (RIM) and others appropriate to the needs and priorities of the organisation.
The IG Steering Committee should have a suitable Chair to ensure the Committee:
- is collaborative to ensure that those members of the committee lead their respective areas to break down information silos with a culture of information and data collaboration;
- is well-structured, meets regularly, and has a clear agenda that is implemented and achieved.
National Archives of Australia
The National Archives has an Information Governance Steering Committee (IGC) which has been assigned by the Director-General to the Archives’ peak governance body, the Executive Board. The terms of reference set out that, ‘[t]he Executive Board added formal responsibility for Information Governance oversight to its role in October 2015 to ensure that the Digital Continuity 2020 Policy is implemented within the Archives and targets for agencies are met’. The National Archives has clear terms of reference for its IGC with defined functions, which provide a useful point of reference for organisations in the process of establishing a Steering Committee.
Steering Committee functions
The role of the Information Governance Steering Committee is to:
- monitor effectiveness of the information governance framework, and all information strategy, policy and architecture documents
- ensure coordination of the information governance reporting and external information audits and reviews
- identify who is responsible within the organisation for information assets identified in audit and review processes
- develop an information management workforce plan with support from the People Management and Development section
- monitor information infrastructure according to the organisation’s business information needs
- coordinate internal information reviews to identify information assets and their value, manage risk and compliance, and improve business processes
- ensure that the organisation’s information is managed for its entire life in accordance with risk, including risks associated with security, access, privacy, continuity, and cost
- ensure coordination of information standards implementation, for example, business systems functionality, metadata and interoperability capabilities
C-level executive who is also responsible for IG
This is a current C-level executive, such as a CEO, COO, GC, CPO or CISO who also is responsible for Information Governance. The way in which the organisation structures Information Governance leadership will be determined by its:
- strategic priorities, size, structure, resources; and
- the stage of Information Governance development within the organisation – that is, whether it is nascent, developing or established.
This model requires the C-level executive to have appropriate leadership skills to work across organisational silos together with sufficient cross-functional expertise to enable them to be an effective Information Governance leader. Determining who will be appropriate to be the overall Information Governance leader will vary from organisation to organisation and will depend on the requirements of the organisation, breadth of cross-functional experience and leadership skills that are determined to be key at the time of the appointment. Types of approaches may include:
- CISO with experience in responding to cyberattacks and data breaches, and the identification, retrieval and production of electronic documents and data in litigation and regulatory inquiries. This would be a CISO who is experienced in working in cross-functional teams, including the privacy and legal teams, and understands the demands and requirements involved regulatory responses;
- CPO with significant data breach responses and information security/cybersecurity experience. This would be a CPO who works closely with the CISO and IT team, and/or a CPO who works closely with Data Analytic team(s) and/or Product Development team(s);
- GC who is experienced in eDiscovery, data breach and broadly understands data analytic technologies and the important opportunities they present to the organisation.
A key issue for the organisation in adding Information Governance leadership responsibilities to the existing responsibilities of the C-level executive is whether they are able to adequately lead Information Governance as well as effectively discharge the responsibilities of their current position. This will depend on whether the additional responsibilities will be supported by the necessary resourcing to support their CIGO role and their current position, and whether they are able to delegate, as appropriate, current responsibilities to ensure they can dedicate sufficient time to their Information Governance responsibilities.
Mastercard
Mastercard implemented an Information Governance program beginning in 2013 to assist with the digital transformation of the organisation at that time. Ms JoAnn Stonier leads the Information Governance and Privacy program for Mastercard on a worldwide basis.
Ms Stonier explains that, ‘MasterCard continually works on building information governance into all of its data and product development efforts. As Mastercards’s business uses of data have changed, our information governance and data privacy team has gone from a team of me to a team of over 40 individuals who are imbedded with our business partners in order to improve our data practices every day. Along the way, we’ve evolved from gate keeping function to one that is more integrated with our business teams which allows us to build and improve our data strategy and develop solutions that enable the growth and advancement of our business.’
Ms Stonier sees the role of Chief Information Governance officer as, ‘leading strategy, building infrastructure, working with regulators, building partnerships, and defining best practices’.
Transpower
Transpower is the owner and operator of New Zealand’s national electricity transmission grid. It also operates the country’s wholesale electricity market. As a critical infrastructure provider, Transpower is part of New Zealand’s earthquake disaster response strategy, requiring a strong focus on accurate real-time asset information for business resilience and the continuing safety of their staff and service providers.
Information Governance is led by the Chief Executive who sets the expectations and behaviours for everyone in the business by acknowledging the essential role data and information plays in underpinning every decision in the business. Transpower business relies heavily on robust records management. Ms Carol Feuerriegel, Enterprise Information Manager explains that, ‘long timeframes (5 to 25 years) for forecasting, planning and constructing transmission electricity infrastructure, combined with rapidly emerging alternative power sources, means Transpower needs to leverage reliable historical data and sophisticated predictive capabilities to make strategic investment decisions for the future’.
Ms Feuerriegel says, ‘ensuring good information and data quality is achieved through Transpower’s Information Governance methodology, includes an internally-consistent information hierarchy, driven from the top-down which identifies accountabilities and decision rights and prioritises the key data elements, core documents, and critical systems required to run the business. This integrated framework of enterprise information assets and accountabilities and the IG methodology becomes the touchstone for all information and data – related decisions.’
Reliability, safety, transparency and auditability are the key drivers in Transpower’s enterprise Information Governance strategy. Ms Feuerriegel explains that, ‘developing effective mechanisms for ensuring authoritative information is available in the right format to everyone who needs it when they need it, requires active participation by every level in the business from the Chief Executive to our people in the field. Given the industry we operate in, our people must be able to trust the information they have available in order to operate safely and efficiently.’
University of Western Australia
Mr Andy Lavender formerly of oil and gas major Chevron and now Associate Director, for Information Governance and Reporting at The University of Western Australia believes the institution has demonstrated a sharper focus by advancing information governance through its Office of Strategy, Planning and Performance. He says, ‘this transformation has provided an opportunity to secure sponsorship at the executive management level.
Mr Lavender is convinced, ‘an ambitious and effective executive sponsor makes all the difference when delivering cross-organisation and organisation-wide programme of works, such as those involving information governance initiatives.’
Designated Chief Information Governance Officer (CIGO)
This is the creation of a new C-level role – the Chief Information Governance Officer. The Information Governance Initiative (IGI), a US IG think-tank describes the CIGO’s role as ‘to balance the stakeholder interests from each facet of IG and develop the right operational model for the organization.’[1]
The Director-General of the National Archives of Australia has called for Federal government agencies to establish a CIGO role to bring people, technology and processes together. Mr David Fricker, Director- General has said,
‘Under its Digital Continuity 2020 policy, the National Archives recognises the role of chief information governance officer as ‘best practice’ for agencies committed to professional information management. As well as leading information governance across an agency, the role is critical for digital innovation and capability, and for championing the importance of effective information management.
An enterprise-wide view will break down silos to create new opportunities to deliver better business outcomes.’
The diagram below illustrates the leadership and co-ordination role of the CIGO to ensure that organisational goals and objectives are met by aligning the areas responsible for data and information throughout the organisation.
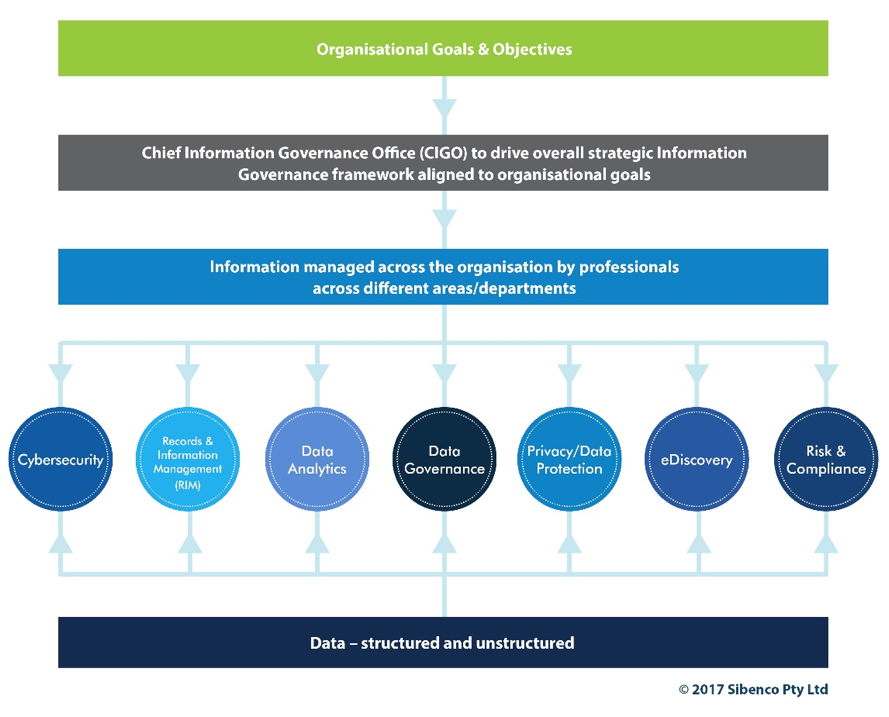
What is the CIGO role?
The CIGO is responsible for ensuring that information facets and the various departments responsible for data and information are aligned and working efficiently and effectively to minimise costs and risks and optimising value from information held throughout the organisation.
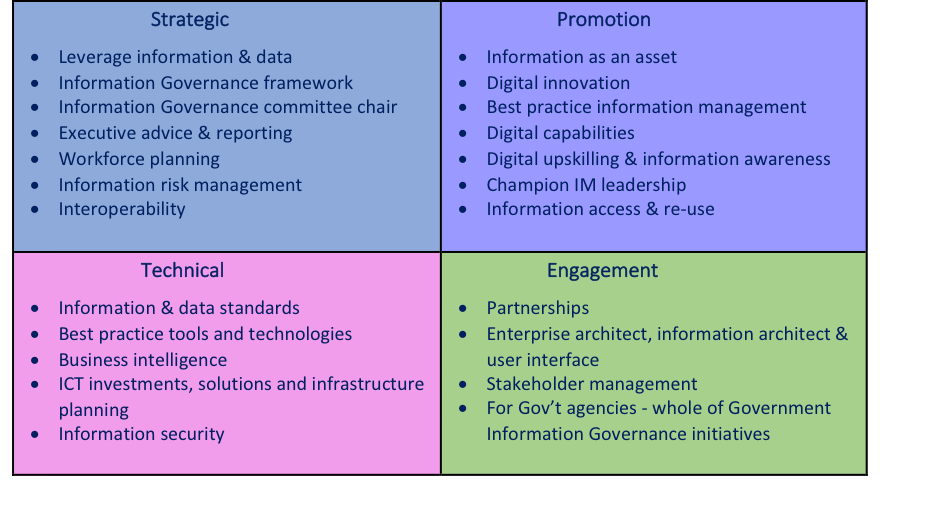
The National Archives divide the CIGO’s responsibilities into 4 areas – strategic, technical, promotion and engagement. The following table sets out CIGO’s responsibilities – this of course will vary from organisation to organisation and will be impacted by strategic priorities, size, structure and resources.
While the role of the CIGO needs to fit the needs of the organisation, the ability of the CIGO to be an effective leader to work with leaders and those responsible for data and information across the organisation will be key to the success of Information Governance. The CIGO will also need to have the confidence of the Board of Directors and the CEO so that resources and priorities will enable an Information Governance program to be effectively implemented that meets:
- legal and regulatory requirements;
- organisational standards and values including ethical and socially responsible standards and/or values of the organisation;
- overall organisational strategic business goals and objectives.
In conclusion
There are different types of Information Governance leadership models – the key is to select the model that is best suited to your organisation’s needs to enable strategic and cost-effective governance of information and data as well achieve overall organisational objectives.
A well-executed Information Governance framework and program, with appropriate leadership should deliver effective security and control of data and information by minimising risks and reducing costs of holding information and maximising the value of information held by the organisation.
Effective Information Governance leadership will enable the organisation to deliver continual strategic and proactive governance as digital disruption impacts the organisation and digital transformation continues.
[1] Information Governance Initiative, Annual Report 2014, p28.
Susan Bennett LLM(Hons), MBA
Principal of Sibenco Legal & Advisory and co-founder of Information Governance ANZ
 Effective leadership of information governance (IG) is key to ensuring that appropriate strategies, priorities, policies and processes are successfully embedded in an organisation, both to maximise the opportunities and minimise the risks arising from the information it holds.
Effective leadership of information governance (IG) is key to ensuring that appropriate strategies, priorities, policies and processes are successfully embedded in an organisation, both to maximise the opportunities and minimise the risks arising from the information it holds.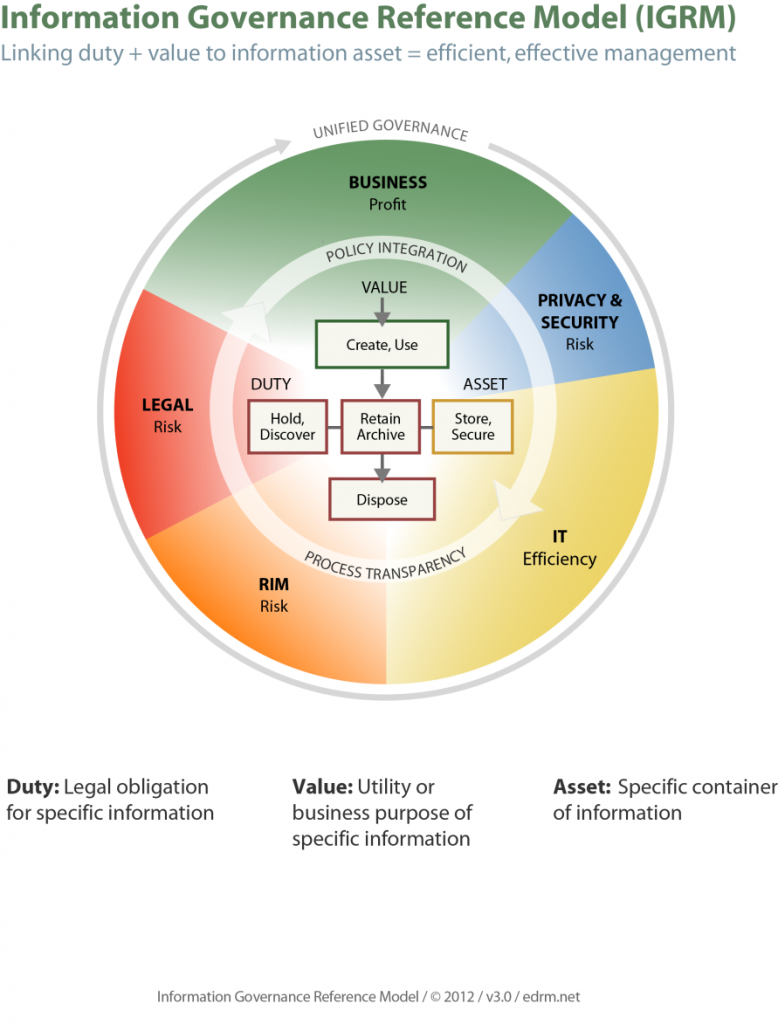
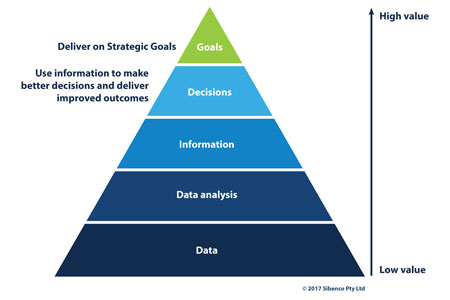 The terms ‘information’ and ‘data’ are often used interchangeably but there are differences in meaning. This article provides an overview of why both Information and Data Governance are important for organisations seeking to control and secure information and an understanding of what each discipline does and achieves for an organisation.
The terms ‘information’ and ‘data’ are often used interchangeably but there are differences in meaning. This article provides an overview of why both Information and Data Governance are important for organisations seeking to control and secure information and an understanding of what each discipline does and achieves for an organisation. As Information Governance and Data Governance becomes increasingly important for organisations seeking to control and secure information, it is important to understand what each one does and achieves.
As Information Governance and Data Governance becomes increasingly important for organisations seeking to control and secure information, it is important to understand what each one does and achieves.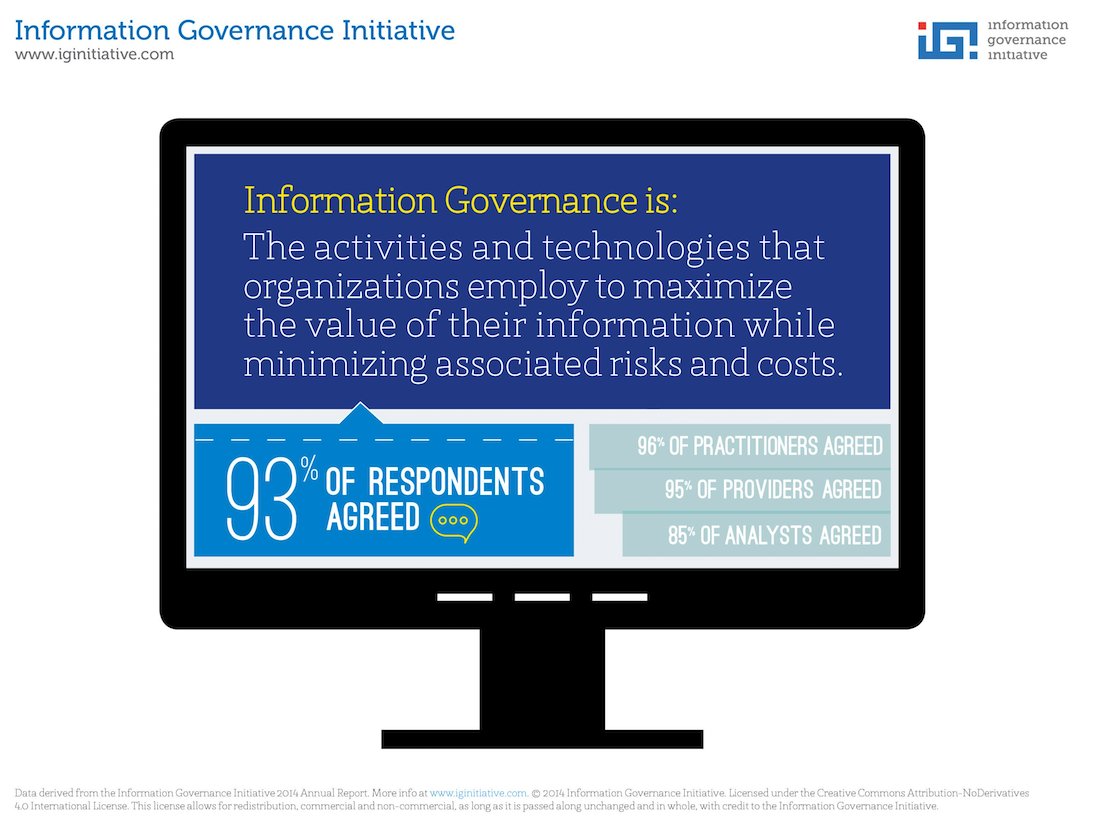
 The Information Governance Imperative
The Information Governance Imperative Preventing data privacy breaches is becoming increasingly important, with the increasing costs of dealing with cyber attacks, IT security breaches, and the subsequent legal actions and regulatory investigations. Strong IG, including privacy governance, is the most effective way to put in place robust systems to prevent and minimise privacy breaches, as well as respond to any privacy breaches that may occur.
Preventing data privacy breaches is becoming increasingly important, with the increasing costs of dealing with cyber attacks, IT security breaches, and the subsequent legal actions and regulatory investigations. Strong IG, including privacy governance, is the most effective way to put in place robust systems to prevent and minimise privacy breaches, as well as respond to any privacy breaches that may occur.